Introduction
Delving into the world of cryptography, you might encounter the perplexing ‘Padding is Invalid and Cannot be Removed’ error during encryption and decryption processes. This error is a sign of a conflict in the cryptographic procedure, which could arise from a variety of issues such as key inconsistencies, improper padding mode configurations, or data integrity problems. In a recent incident reported by The Register, organizations faced a dreadful situation where after succumbing to the demands of ransomware attackers and paying for decryption keys, they found themselves unable to decrypt their files due to errors, presumably like the ‘Padding is Invalid’ error.
This highlights the critical importance of understanding and correctly implementing encryption standards to avoid catastrophic data loss. Encryption is not only about securing data but also about ensuring that it can be accurately decrypted by authorized users. As emphasized by industry experts, the application of robust encryption measures is essential in fields such as banking and healthcare, where Java applications frequently manage sensitive information.
In this article, we will explore the common causes of the ‘Padding is Invalid and Cannot be Removed’ error, the importance of consistent encryption and decryption keys, the impact of incorrect padding mode settings, the handling of concatenated or corrupted data, and steps to resolve the error. By understanding these key aspects and following best practices, you can enhance the security and integrity of your encryption processes.
Understanding the ‘Padding is Invalid and Cannot be Removed’ Error
Exploring the realm of cryptography, you may come across the puzzling ‘Invalid Padding and Unable to Remove’ issue during the process of encoding and decoding. This error is a sign of a conflict in the cryptographic procedure, which could arise from a variety of issues such as key inconsistencies, improper padding mode configurations, or data integrity problems. The beginnings of encoding go back to the 1500s with polyalphabetic ciphers, which encoded messages by dividing them into blocks and substituting symbols based on a secret key. Modern cryptography adheres to a comparable block-based structure, and padding ensures that each block reaches the necessary size for the encryption algorithm. However, if the padding is misaligned with the decryption process, it can prevent the original message from being accurately retrieved.
In a recent incident reported by The Register, organizations faced a dreadful situation where after succumbing to the demands of ransomware attackers and paying for decryption keys, they found themselves unable to decrypt their files due to errors, presumably like the ‘Padding is Invalid’ error. This emphasizes the vital significance of comprehending and accurately executing security measures to prevent disastrous information loss. Encryption is not only about securing information but also about ensuring that it can be accurately decrypted by authorized users. As emphasized by industry experts, the application of robust encryption measures is essential in fields such as banking and healthcare, where Java applications frequently manage sensitive information.
In the context of information transmission, particularly across systems that may only recognize ASCII information, base64 encoding plays a crucial role. The encoding process converts binary information into ASCII text format, enabling its safe traversal through network environments that may not support binary information. This is particularly relevant for emails and other legacy systems where encoding non-text attachments is necessary. Moreover, with the emergence of cloud computing and the widespread use of software applications, ensuring information security across platforms has become a crucial challenge. Companies such as Thales have highlighted the importance of reliable security measures to protect information in the cloud and guarantee safe usage of applications and APIs.
In general, a comprehensive understanding of encryption processes, along with diligent implementation and troubleshooting, is paramount in protecting digital assets and maintaining integrity across various platforms and applications.
Common Causes of the Error
Comprehending and resolving ‘Padding is Invalid and Cannot be Removed’ issues are crucial in preserving data integrity during synchronization processes. As seen in real-life situations, like Active Directory synchronization with Microsoft Entra ID, problems can occur when attributes contain repeated values or fail to meet formatting requirements, leading to the aforementioned issue. Additionally, this issue is not exclusive to directory synchronization; it can also occur during device updates or restorations, as seen with iTunes 4013 on iOS devices. This issue typically arises from interruptions or hardware failures during the update or restoration process. Software glitches and bugs are also common culprits of such issues, indicating that a good first step in troubleshooting involves updating the software to the latest version. Furthermore, understanding the underlying technical principles, such as Euler’s totient function and theorem in RSA cryptography, can provide insights into the mathematical structures that protect sensitive information and the potential points of failure. By examining these instances and guidelines, an individual can formulate a holistic strategy to address ‘Padding is Invalid and Cannot be Removed’ issues and guarantee the smooth transmission of precise information among systems.
Mismatched Encryption and Decryption Keys
The ‘Padding is Invalid and Cannot be Removed’ issue is often a clear indication of a deeper underlying problem: the misalignment of encoding and decoding keys. At its core, this issue arises when the key that secures the data (security key) doesn’t match the key attempting to unlock it (decryption key). Just like a mismatched key to a treasure chest, if they don’t align perfectly, access is denied, resulting in the aforementioned error.
To unravel this problem, consider the scenario where a king must ensure that only he can access the kingdom’s crown jewels. If the key to the chest is mishandled or replaced, the chest remains locked, reflecting the security conundrum. The importance of maintaining a consistent encryption-decryption key pairing cannot be emphasized enough, as even a minor discrepancy can make information inaccessible.
In the digital realm, encryption key discrepancies can lead to severe outcomes similar to the Marvin Attack, where even a slight variance in the decryption process can be exploited, revealing the contents to unintended parties. Statistics reveal that 83% of organizations have experienced breaches due to compromised credentials, highlighting the necessity for strict key management protocols.
Moreover, recent incidents have demonstrated the catastrophic implications of key mismatches. For instance, victims of the Hazard ransomware, after giving in to ransom demands, were left with a decryptor that failed to function due to key inconsistencies, resulting in irreversible loss of information.
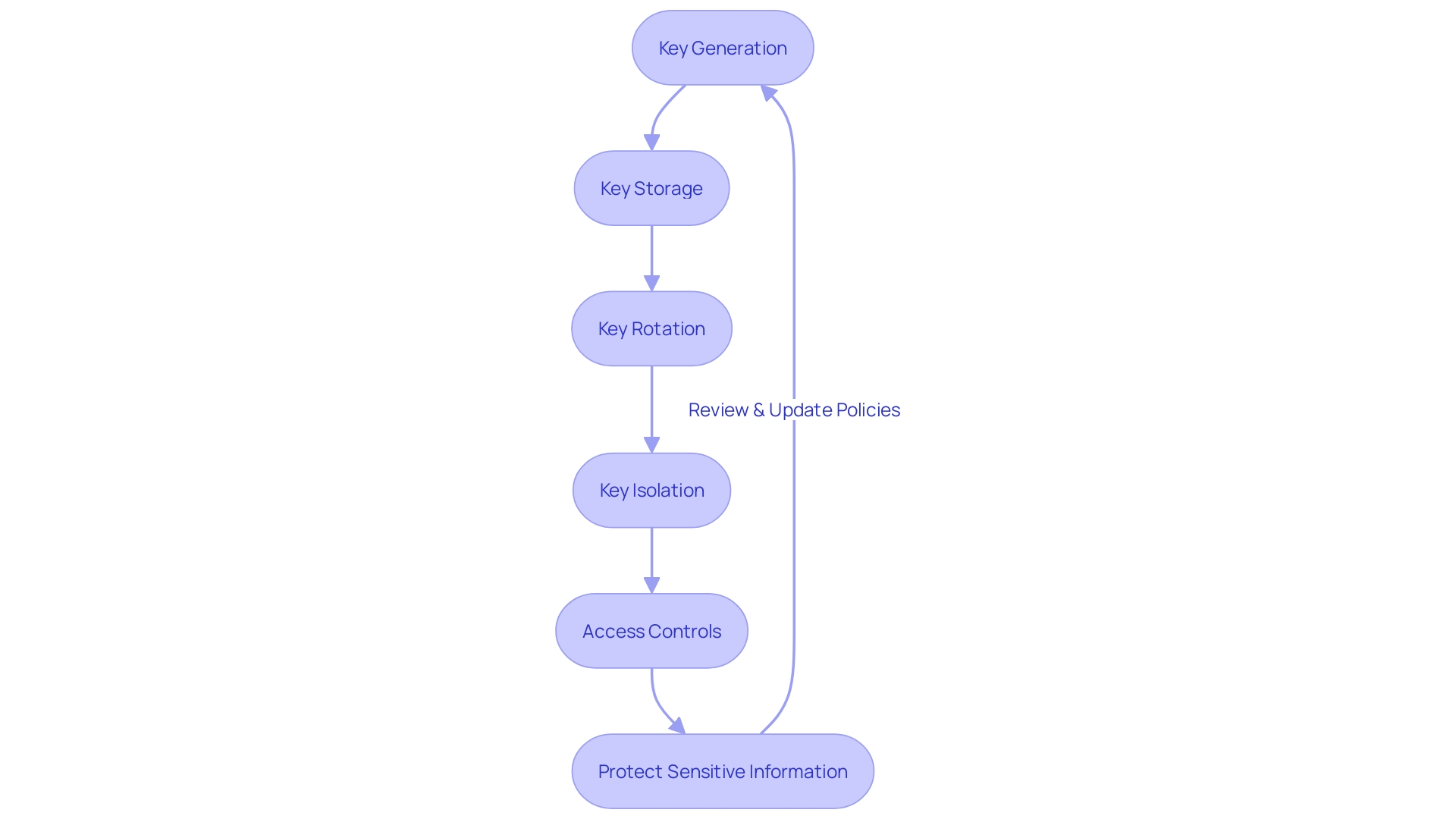
To reduce such risks, it is crucial to uphold a watchful and systematic approach to key management, guaranteeing that the integrity of the encoding process remains intact from generation to application. This not only safeguards sensitive data but also fortifies the organization’s defense against complex cyber threats.
Incorrect Padding Mode
Mismatched padding modes can cause the notorious ‘Padding is Invalid and Cannot be Removed’ issue, a stumbling block when different decryption and encryption algorithms don’t align. Much like the unexpected twist in a startup’s early days that led to a $10,000 misstep due to a single line of code, incorrect padding settings can be a subtle yet critical error to catch. By closely examining and realigning the padding mode settings, similar to scrutinizing sentry logs or revisiting key files in the hunt for a bug, one can tackle and troubleshoot this security challenge effectively. It’s a delicate dance of settings that, when matched, ensure smooth and secure transactions, much like finding the perfect riding posture after a long quest for the right motorcycle upgrade. When it pertains to securing data, every detail is important, and aligning the padding modes can be the key to unlocking a seamless, secure operation.
Concatenated or Corrupted Data
In the realm of information management, the encryption and decryption processes are critical for safeguarding sensitive details. Nevertheless, the integrity of the encrypted information is crucial. Problems arise when this information becomes concatenated or corrupted, either in transit or storage, leading to errors such as ‘Padding is Invalid and Cannot be Removed’ during decryption attempts. To address these concerns, one must ensure proper handling of joined information and maintain the integrity of the information throughout the process.
Batch processing provides insights into effectively managing such challenges. This approach involves gathering, retaining, and converting information at consistent intervals, which is crucial for upholding the precision and dependability of the information flow. For instance, using batch processing, information from OCR files containing shopping bills information can be accurately extracted and reconstructed into individual files, preserving the integrity of each transaction’s details.
Moreover, progress in information storage and safeguarding, such as those by Project Silica, which employs quartz glass to retain information indefinitely, emphasize the significance of secure and unchangeable information administration techniques. Implementing Azure AI in this project to decode information stored in glass showcases the cutting-edge integration of AI with information protection, ensuring the security and integrity of information.
In our interconnected world, the management of information is not only a technical matter but a duty towards stakeholders and consumers, as highlighted by DE-CIX’s role in the smooth, rapid, and safe exchange of information. Thus, it’s crucial to adopt robust strategies for data integrity, learning from successful processing models and innovative storage solutions to prevent and address issues like corrupted or concatenated data in encryption systems.
Steps to Resolve the Error
Addressing the ‘Padding is Invalid and Cannot be Removed’ issue requires a careful and systematic approach. If your Active Directory (AD) synchronization to Microsoft Entra ID is not functioning as expected, leading to sync issues and messages that indicate either a duplicate attribute value or a violation of formatting requirements, you can start by investigating these issues. Use these steps to identify and fix the problem:
- Check if the attribute values are unique and meet the formatting criteria such as character set and length, as these are common sources of errors during AD synchronization.
Examine the prerequisites and verify that they are steady and comprehended, to avoid misconfigurations that might result in mistakes. - Consider software modularity in your troubleshooting approach, focusing on decoupling and cohesion to isolate the issue.
It’s important to be aware of the context in which the error occurs, whether it’s local to a class or at the system level. By addressing these factors, you can enhance both the performance and development experience, leading to more readable and maintainable code. Remember that your feedback is valuable, so if you’ve resolved the issue or need further assistance, please use the Feedback button to share your experience or seek additional help.

Ensure Consistent Encryption and Decryption Keys
To maintain the security and integrity of digital communication, especially in sensitive fields like finance and healthcare, the use of cryptographic techniques is a critical tool. Encryption transforms plain, readable information into a coded format, unreadable to anyone without the proper decryption key, effectively shielding it from unauthorized access. The success of this procedure relies on the careful handling of encryption and decryption codes. It is crucial that the appropriate keys are utilized for their corresponding procedures to guarantee information remains safeguarded and available to authorized individuals. This is not just a technical detail but a fundamental element of security.
As we explore the technical domain of secure coding, it’s crucial to grasp that employing consistent keys for encoding and decoding is not only recommended but necessary. Should there be a discrepancy, the consequences could range from information being temporarily inaccessible to being permanently lost or compromised. Such scenarios are not theoretical; they have occurred in real-world situations, highlighting the critical nature of key management.
This requirement is emphasized by the notion of a cryptoperiodâthe duration for which a specific security key is authorized for use. A well-defined cryptoperiod aims to limit the exposure if a key is compromised and to constrain the amount of data available for cryptanalysis that could potentially reveal the key. These measures are a testament to the delicate balance that must be struck between accessibility and security in the digital landscape.
Hence, when handling the process of securing confidential information, one must guarantee that they are consistently implemented throughout their lifecycle. The keys must be securely stored, routinely changed within their cryptoperiod, and correctly paired for the process of encoding and decoding. This carefulness is a foundation of preserving the strength of safeguarding as a protective measure against breaches and unauthorized entry.
Verify Padding Mode Settings
To preserve the integrity and security of your information during encryption and decryption, it is essential to verify the compatibility and consistency of the padding mode settings. Mismatched padding modes can lead to decryption errors, compromising information security. If discrepancies are found, adjusting the padding mode settings is essential to ensure a seamless and secure exchange of information, particularly when dealing with cross-platform interactions between systems like. NET Framework C# and Java. In the realm of digital security, the significance of utilizing strong coding cannot be emphasized enough, given the diverse applications of Java across industries. Symmetric algorithms like AES are widely recognized for their fast and secure nature, making them an excellent option for safeguarding sensitive information. However, with the advent of quantum computing, the landscape of digital security is evolving, necessitating the development of post-quantum cryptography to safeguard against future threats. As such, staying informed about the latest advancements and maintaining up-to-date encryption practices is paramount for ensuring the long-term protection of digital assets.

Handle Concatenated Data Properly
In the realm of digital security, the management of encrypted information is a paramount concern, particularly when dealing with concatenated datasets that can complicate decryption processes. To alleviate potential risks and uphold the integrity of information, it is crucial to deconstruct concatenated data into distinct components before decryption. This approach ensures that each piece of information is properly managed and secured. Additionally, maintaining the integrity of information during its transmission and storage is equally vital, requiring diligent oversight to prevent unauthorized access or breaches. By adopting these strategies, organizations can confidently protect sensitive information in our increasingly connected world.

Example Code Adjustments for Proper Padding
Strengthening code to enhance security can be compared to fortifying the digital armor that protects sensitive information. In the realm of securing and decoding, where the Advanced Encryption Standard (AES) is the stalwart guardian of information, meticulous attention to detail is crucial. Making sure the correct padding in your code is not just a formality, it’s a fundamental aspect of maintaining the integrity of information. Padding modes, which determine how the plaintext is handled prior to the encoding process, must be in perfect accordance with the algorithm’s specifications.
When the information you’re safeguarding is susceptible to the constantly changing cybersecurity threats, staying ahead of the curve is crucial. For instance, the rise of post-quantum cryptography (PQC) is a testament to the foresight needed in this field. PQC is the cryptographic sanctuary designed to withstand the formidable prowess of both classical and quantum computers. The recent support for a PQC algorithm by Chrome is a harbinger of the gradual integration of these advanced cryptographic defenses into mainstream applications.
Including error handling mechanisms to address concatenated or corrupted information further strengthens the encryption procedure. It’s a proactive measure, ensuring that even if the information’s integrity is compromised, the security measures in place can identify and rectify the issue promptly. The complexity of this task is underscored by the nuanced challenges posed by Fully Homomorphic Encryption (FHE) research, where designing efficient information packing and optimizing computational models is at the forefront.
Encryption is the invisible yet impenetrable barrier that keeps Java applications across banking, healthcare, and numerous other sectors secure. Whether the data is stored in the cloud or is in transit, organizations like Thales emphasize the importance of strong security measures to prevent data breaches and maintain compliance. With the world’s reliance on cloud-powered applications and APIs, making sure the code for protecting information is up to the task is not just prudent—it’s imperative.
As you delve into the encryption code, remember that it’s not just a sequence of commands—it’s the shield that protects the very essence of privacy and security in our digital world. Take the time to review and refine the code, and you’ll contribute to a safer digital environment for all.
Troubleshooting Checklist
When faced with complex system integrations or troubleshooting web services, it’s imperative to have a streamlined process for diagnosing issues. Let’s take the example of Oracle databases integrating with web services via PL/SQL code. If you encounter issues, particularly with HTTPS protocols, having a checklist ensures you don’t miss critical steps. Similarly, with XM Cloud applications, ensure your site tracks visitors correctly. An empty insights chart indicates a tracking problem; utilize browser development tools and the Network tab for deeper insight.
Imagine you’re rerouting requests to a new server with an updated Nginx configuration, only to find a malfunctioning UI. This scenario calls for a systematic review, starting with the network tab. Investigations might reveal that the environment settings on your computer are different, affecting the code’s performance. Here’s a non-exhaustive list to check:
- Verify recent changes in diet or the need for a break.
- Increase log details to isolate the issue.
- Confirm the correct environment (local/staging, etc.).
- Inspect specific functions for expected behavior.
A structured approach can save time and frustration, as seen in Ubisoft’s case with Assassin’s Creed Shadows. By extending the development time, they allowed for a thorough debug and adaptation based on feedback, illustrating the importance of a detailed checklist during the debug, checkout, and startup process.
Moreover, it’s beneficial to keep a dashboard to monitor active feature flags and promotions. Understanding system elasticity and knowing when to enhance capacity and throughput is crucial. Keeping these aspects in check aligns with the FAA’s recommendation for mechanics to follow a checklist to counter complacency and ensure task accuracy.
Remember, conducting a thorough Root Cause Analysis (RCA) is not only crucial during problems but also when outcomes are unexpectedly positive. It helps understand the factors contributing to success, which is essential for maintaining and enhancing application software as substantial resources are devoted to this phase.
In summary, whether you are debugging an integration issue or ensuring the proper functioning of a complex system, a well-thought-out troubleshooting checklist is an indispensable tool. It guides you through the process, helping identify and resolve problems efficiently and effectively.

Best Practices for Avoiding the Error in the Future
To navigate the complexities of coding and ensure a seamless user experience, it’s crucial to adopt proven methods that mitigate common issues such as ‘Padding is Invalid and Cannot be Removed’. Reflecting on past experiences, such as a start-up’s early challenges with monetization bugs, reveals the importance of meticulous code review and testing. Even a single line of code, seemingly harmless, can unravel into a costly mistake, as was the case where a mishandled line led to a $10,000 mistake. This underscores the necessity of thorough testing and monitoring, particularly in high-stakes environments like rushed updates to a client’s Single Page Application (SPA) before a significant sale event.
Responsive design principles further emphasize the need for precision in coding practices. When implementing designs that adapt to various devices and user settings, such as text resizing or window adjustments, understanding the difference between absolute and relative units becomes paramount. Absolute units maintain consistency across different contexts, whereas relative units adjust based on other elements, like font size or viewport dimensions. This distinction is critical when ensuring that content and spacing remain accessible and legible under any condition.
Moreover, the CSS Box Sizing property plays a vital role in managing an element’s dimensions, considering padding and borders. Choosing between ‘content-box’ and ‘border-box’ values can drastically affect the layout and functionality of a web page. Developers must leverage these tools thoughtfully to create resilient, user-friendly sites.
Feedback from users and data synchronization issues, as noted in prompts for user input and AD DS objects, highlight the importance of responsive and adaptable systems. While the information collected by cookies helps tailor user experiences, it’s equally important to respect privacy preferences and understand the implications of blocking certain types of cookies on website functionality.
Finally, the Marvin Attack analogy reminds us that even the most secure systems can exhibit vulnerabilities. Similar to a lock that behaves differently based on its contents, code must be crafted and tested to withstand unexpected conditions and potential security threats. Adopting these best practices will not only prevent future errors but also fortify the overall robustness of web projects.
Conclusion
In conclusion, understanding and addressing the “Padding is Invalid and Cannot be Removed” error is crucial for maintaining data integrity and security during encryption and decryption processes. This error can arise from various issues such as key inconsistencies, improper padding mode configurations, or concatenated and corrupted data.
To mitigate this error, it is essential to ensure consistent encryption and decryption keys. Mismatched keys can lead to data inaccessibility or compromise, emphasizing the need for stringent key management protocols. Similarly, verifying and aligning the padding mode settings is crucial for a seamless and secure data exchange.
Proper handling of concatenated or corrupted data is also vital to prevent decryption errors. By deconstructing concatenated data into distinct components and maintaining data integrity, organizations can protect sensitive information effectively.
Resolving the “Padding is Invalid and Cannot be Removed” error requires a deliberate and methodical approach. Troubleshooting checklists, such as verifying attribute values and reviewing requirements, can help identify and fix the problem. Additionally, adopting best practices like thorough code review, testing, and following responsive design principles can prevent such errors in the future.
By understanding these key aspects and implementing best practices, organizations can enhance the security and integrity of their encryption processes. Encryption is not just about securing data; it is about ensuring that authorized users can accurately decrypt it. With the increasing reliance on digital communication and data handling, robust encryption measures are essential to protect sensitive information and defend against complex cyber threats.
Implement best practices and enhance the security and integrity of your encryption processes.